SSH public key distribution with dokuwiki and lbows
That’s an interesting title, eh? You wonder „ssh public key distribution“ with **dokuwiki**? Yes. Keep reading.
**Task**: Create a simple and lean SSH key distribution solution for multiple linux-servers. Do this quick and don’t spend much time doing it.
**Why**: We need a simple solution to distribute ssh public keys of people allowed to access certain servers and keep that updated as easy as possible. And we need a nice overview of the current situation at any times.
===== The dokuwiki-part =====
First thing to think about is a UI for this. Having the task to not spend much time thinking about it, I came to a very simple but IMHO really sophisticated method:
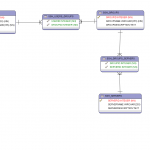
We naturally need some kind of database for this. The keys should be stored and the connection between the key and a server should be done. That’s a very simple database layout.
For the UI-part we need a simple [[http://en.wikipedia.org/wiki/Create,_read,_update_and_delete|CRUD]]-solution for this database, nothing more. We’re using a [[http://www.dokuwiki.org|dokuwiki]] at our site and I came across the wonderful [[http://www.dokuwiki.org/plugin:database2|Database2-plugin]]. With this plugin you can easily create a CRUD-UI for any [[http://de3.php.net/manual/en/book.pdo.php|PDO-enabled database]] very quickly.
So I created the following database design:
(I actually used database2 and it created the tables for me. Did I mention, that it was a neat plugin?)
That completes the UI.
===== The lbows-part =====
My „baby“ [[http://www.lbows.org|lbows]] was used for the second part: Bringing the keys to a form like the //authorized_keys//-file used by SSH to the server. That should’nt include much requirements on the server side. A simple download would be great.
I created a small lbows module for that (see [[https://github.com/dploeger/lbowsmodules/wiki/SshKeyDistribution]]) and even updated lbows‘ rest module to handle my requirement (so if you want to use it, you’ll have to update lbows).
After installing and configuring, I got my backend server for the key distribution. My „key distribution center“, if you like and the kerberos guys don’t kill me.
===== The server-part =====
On the server I would simply create a cronjob that downloads my authorized_keys file by doing:
wget -q -O- „http://lbows/index.php/SshKeyDistribution/rest/getAuthorizedKeys/`hostname -s`?response“ > /root/.ssh/authorized_keys
Nice.
===== Conclusion =====
When it comes to complex administrator tasks, it’s often wise to use the KISS-strategy („Keep it simple, stupid“; whereas some folks rather say „Keep it simple, sweetie“). Some complex tasks are actually very simple if you think outside the box.
Calendar
| M | D | M | D | F | S | S |
|---|---|---|---|---|---|---|
| 1 | 2 | 3 | 4 | 5 | 6 | |
| 7 | 8 | 9 | 10 | 11 | 12 | 13 |
| 14 | 15 | 16 | 17 | 18 | 19 | 20 |
| 21 | 22 | 23 | 24 | 25 | 26 | 27 |
| 28 | 29 | 30 | 31 | |||
Archive
- Januar 2024
- Dezember 2023
- April 2021
- März 2021
- September 2020
- Dezember 2019
- November 2019
- Oktober 2019
- Juli 2019
- Juni 2019
- Mai 2019
- April 2019
- März 2019
- September 2018
- August 2018
- Juli 2018
- März 2018
- Januar 2018
- Dezember 2017
- September 2017
- März 2017
- Februar 2017
- Januar 2017
- August 2016
- Mai 2016
- Dezember 2015
- November 2015
- August 2015
- März 2015
- Dezember 2014
- September 2014
- August 2014
- Juli 2014
- Februar 2014
- Oktober 2013
- September 2013
- August 2013
- Juli 2013
- Juni 2013
- Mai 2013
- April 2013
- November 2012
- Oktober 2012
- September 2012
- August 2012
- Juni 2012
- Mai 2012
- März 2012
- Februar 2012
- Januar 2012
- November 2011
- Juli 2011
- Juni 2011
- März 2011
- Februar 2011
- Januar 2011
- Dezember 2010
- November 2010
- April 2010
- Februar 2010